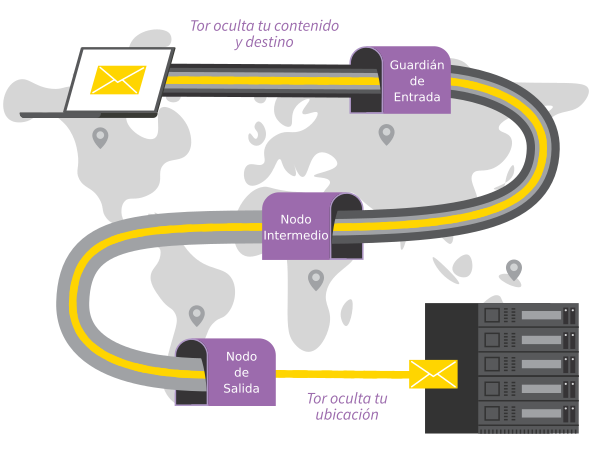
Todo lo que haces en Internet desde Tails pasa por la red Tor.
Tor cifra y anonimiza tu conexión pasándola a través de 3 repetidores. Los repetidores de Tor son servidores operados por diferentes personas y organizaciones en todo el mundo.
No puedes acceder a Internet desde Tails hasta que estés conectado a
Tor. Por ejemplo, el Navegador Tor muestra el mensaje de error El
servidor proxy rechaza conexiones hasta que esté conectado a Tor.
Como Tor enruta tu tráfico de Internet a través de 3 repetidores antes de llegar a su destino, la conexión es más lenta que cuando no estás usando Tor.
Consulta nuestra documentación sobre por qué Tor es lento.
Para conectarse a la red Tor:
Conéctate a una red local, cableada, Wi-Fi, o móvil.
El asistente Conexión Tor aparece para ayudarte a conectarte a la red Tor.
Elige si deseas:
Conectar a Tor automáticamente
Ocultar a la red local que estás usando Tor
Las implicaciones de ambos métodos se detallan a continuación.
Tor relays and bridges
Repetidores Tor públicos
La mayoría de las veces, tu red local no bloquea el acceso a la red Tor y puedes usar un repetidor público como tu primer repetidor Tor.
El uso de un repetidor de Tor público como tu primer repetidor Tor le deja claro a tu red local que te estás conectando a Tor, manteniendo tu actividad en línea segura y anónima.
Puentes Tor
Tor bridges are secret Tor relays that hide that you are connecting to Tor.
Utiliza un puente como tu primer repetidor de Tor si la conexión a Tor está bloqueada o si usar Tor podría parecer sospechoso para alguien que monitorea tu conexión a Internet.
La tecnología utilizada por los puentes de Tor está diseñada para evitar la censura donde las conexiones a Tor están bloqueadas, por ejemplo en algunos países con fuerte censura, por algunas redes públicas, o por algunos controles parentales.
Lo hace camuflando tu conexión para que no pueda ser reconocida como una conexión a Tor. Como consecuencia, se puede utilizar la misma tecnología para ocultar que estás usando Tor si pudiese parecer sospechoso para alguien que monitorea tu conexión a Internet.
Los puentes de Tor suelen ser menos fiables y más lentos que los repetidores de Tor públicos.
Connecting to Tor automatically
Recomendamos conectarse a Tor automáticamente si está en una red Wi-Fi pública o si muchas personas en su país usan Tor para eludir la censura.
Cuando eliges esta opción:
Primero, Tails sincroniza el reloj del ordenador automáticamente, porque se necesita una hora correcta para poder conectarse a la red Tor.
Tails learns the current time by connecting to the captive portal detection service of Fedora, which is used by most Linux distributions. This connection does not go through the Tor network and is an exception to our policy of only making Internet connections through the Tor network.
You can learn more about our security assessment of this time synchronization in our design documentation about non-Tor traffic.
Si en su lugar eliges ocultar que te estás conectando a Tor, puede que tengas que arreglar el reloj del ordenador manualmente.
If Tails fails to synchronize the clock because you have to sign in to the network using a captive portal, an error screen is displayed that helps you do so.
For detailed instructions, see how to sign in to the network using a captive portal.
Then, Tails tries different ways of connecting to Tor until it succeeds:
Tails tries to connect to Tor directly using public relays, without using a bridge.
Tails tries to connect to Tor using one of the default bridges, already included in Tails, if connecting using public relays fails.
Tails uses the default obfs4 bridges from Tor Browser.
If public relays and default bridges don't work, Tails asks you to configure a custom bridge.
See configuring a Tor bridge below.
Alguien que esté monitoreando tu conexión a Internet podría identificar estos intentos como provenientes de un usuario de Tails.
Hiding to your local network that you are connecting to Tor
You might need to go unnoticed if using Tor could look suspicious to someone who monitors your Internet connection.
Cuando eliges esta opción, Tails solo se conectará a Tor después de configurar un puente de Tor personalizado. Los puentes son repetidores de Tor secretos que ocultan que te estás conectando a Tor.
It is impossible to hide to the websites that you visit that you are using Tor, because the list of exit nodes of the Tor network is public.
Our team is doing its best to help you connect to Tor using the most discreet types of Tor bridges. That is why, when you decide to hide that you are connecting to Tor:
Tails does not automatically detect whether you have to sign in to the network using a captive portal.
Default bridges are not available.
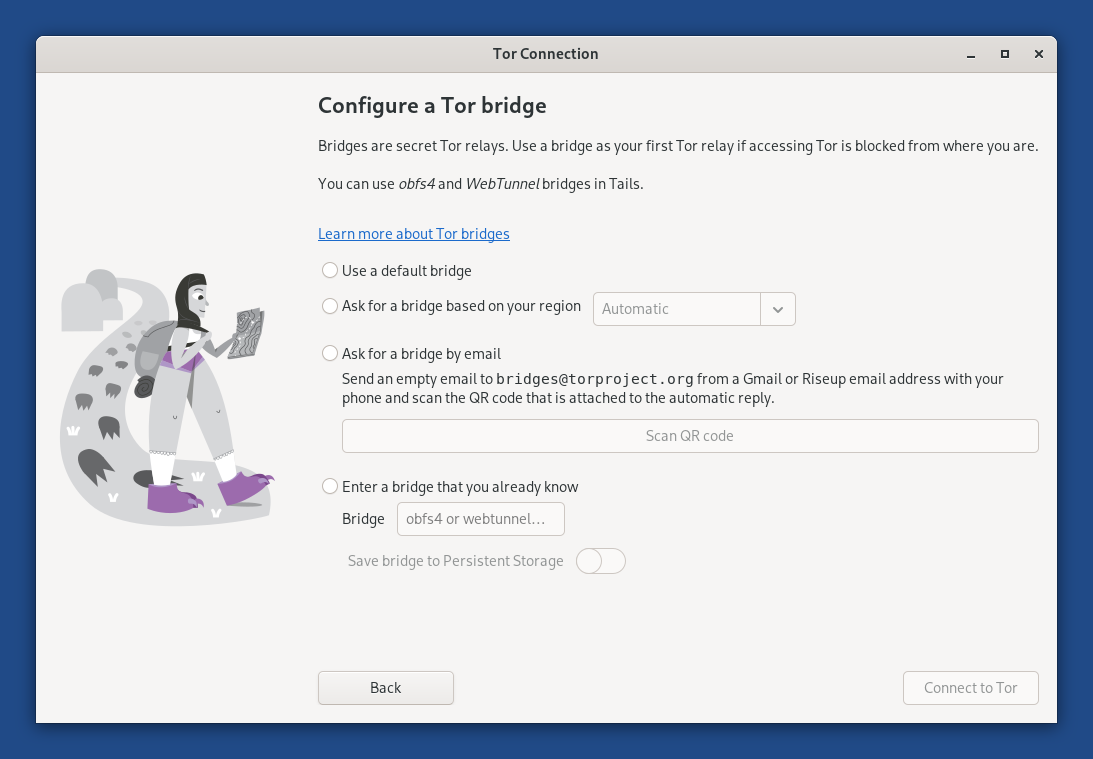
Configuring a Tor bridge
When Tor Connection fails to connect to Tor using public relays and default bridges, select Configure a Tor Bridge from the error screen.
Puedes usar puentes obfs4 y WebTunnel en Tails ahora mismo.
To configure a Tor bridge in Tor Connection, you can either:
Ask for a bridge based on your region
This option is the easiest as it allows you to learn about bridges directly from Tails.
Tails downloads information about bridges that are most likely to work in your region from the Moat API of the Tor Project. To circumvent censorship, this connection is disguised as a connection to another website using domain fronting.
If you choose Automatic as region, the country of your IP address is used.
Ask for a bridge by email
Puedes enviar un correo electrónico vacío a bridges@torproject.org de una dirección de correo electrónico de Gmail o Riseup.
Enviar el correo electrónico revela a Gmail o Riseup que estás intentando conectarte a Tor pero no a alguien que monitorice tu conexión a Internet.
Enter a bridge that you already know
Before starting Tails, learn about bridges by either:
Visiting https://bridges.torproject.org/options.
We recommend that you visit this page from a different local network if accessing this page is blocked or if you want to hide that you are connecting to Tor.
Sending a message to @GetBridgesBot from Telegram.
Store the bridge lines in a text document on separate USB stick for later use in Tails.
After you started Tails, copy one of the bridge lines from this other USB stick into Tor Connection.
Incluso alguien que conoce tu puente no puede saber lo que estás haciendo en línea desde Tails.
To save the last Tor bridge that connected to Tor successfully, turn on the Tor Bridge feature of the Persistent Storage.
Troubleshooting connecting to Tor
Consulta nuestra documentación sobre solución de problemas de conexión a Tor.
Viewing the status of Tor
El estado de Tor aparece como un icono de cebolla en el área de notificación:
 You are connected to Tor.
You are connected to Tor. You are not connected to Tor.
You are not connected to Tor.
To view the list of Tor circuits that are used by your different applications, click on the Tor status icon and choose View Tor Circuits. Learn more about managing Tor circuits.